
“We made a mistake” delaying the Lapsus$ hack disclosure

Okta has admitted that it made a mistake delaying the disclosure of hack from the Lapsus$ facts extortion group that took location in January.
Moreover, the organization has delivered a in depth timeline of the incident and its investigation pursuits.
Okta: “we produced a miscalculation” around late breach disclosure
On Friday, Okta expressed regret for not disclosing details about the Lapsus$ hack faster and shared a thorough timeline of the incident and its investigation.
The hack from the Lapsus$ data extortion group originated at Sitel, Okta’s 3rd-occasion provider of consumer help providers.
“On January 20, 2022, the Okta Safety staff was alerted that a new factor was additional to a Sitel purchaser aid engineer’s Okta account. This factor was a password,” points out Okta.
“Although that unique attempt was unsuccessful, out of an abundance of warning, we reset the account and notified Sitel” who further engaged a foremost forensic firm to accomplish an investigation.
.jpg)
“We want to admit that we produced a oversight,” states Okta, more admitting that it is finally responsible for its contracted provider providers like Sitel.
Okta promises that in January it wasn’t knowledgeable of the extent of the incident which, the enterprise considered, was minimal to an unsuccessful account takeover attempt concentrating on a Sitel assist engineer.
Sitel’s engagement of a forensics business for investigating the incident and making ready a report even more delivered assurance to Okta at the time that the matter required no further more escalation.
“At that time, we failed to realize that there was a possibility to Okta and our prospects. We need to have a lot more actively and forcefully compelled information from Sitel. In light of the proof that we have gathered in the previous week, it is distinct that we would have created a distinct selection if we had been in possession of all of the points that we have currently,” suggests Okta.
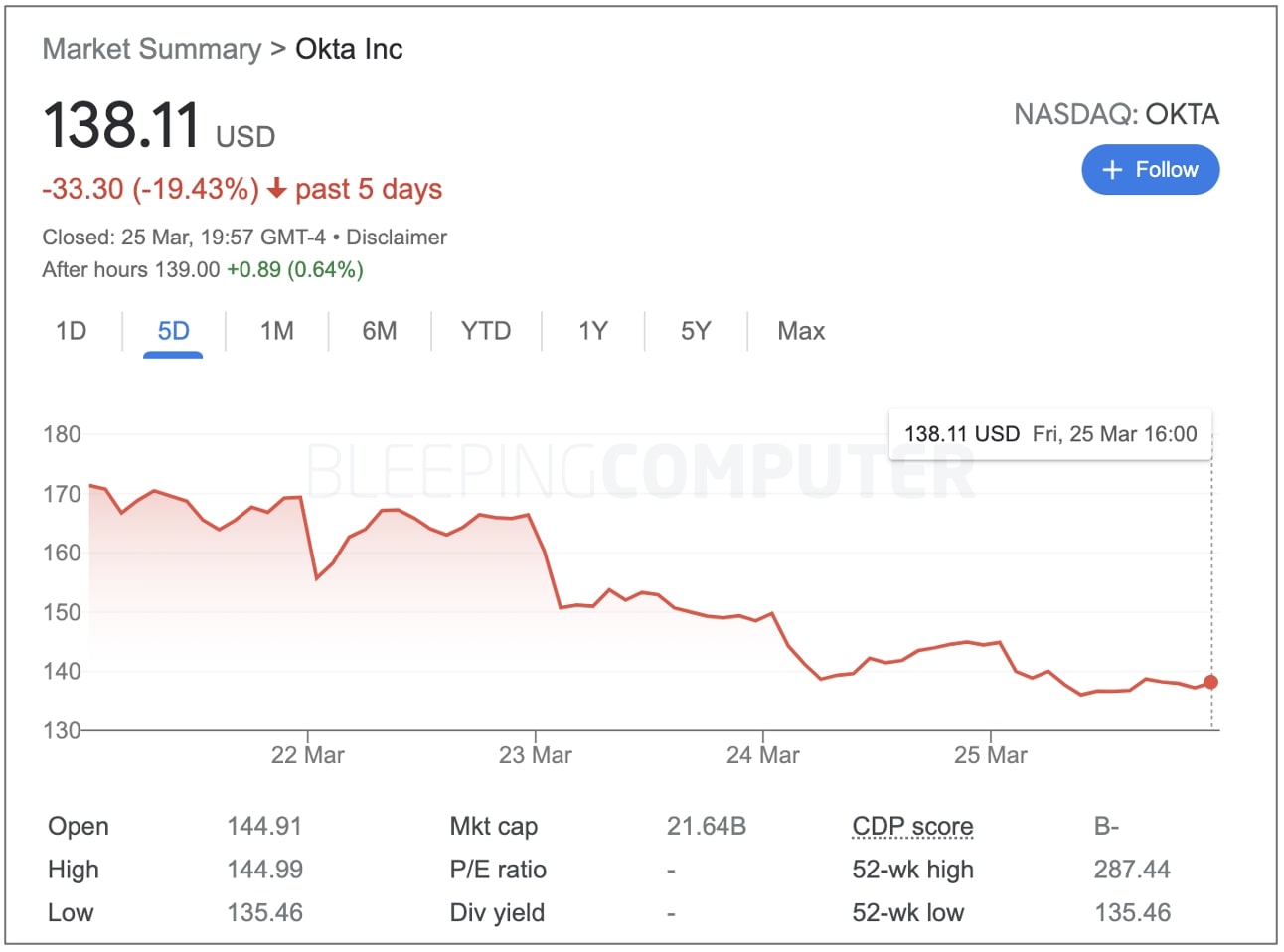
Okta’s shares fell by just about 20{f5ac61d6de3ce41dbc84aacfdb352f5c66627c6ee4a1c88b0642321258bd5462} after disclosure
Subsequent Okta’s haphazard disclosure of the January cyber incident this month, the firm’s inventory price dipped by practically 20{f5ac61d6de3ce41dbc84aacfdb352f5c66627c6ee4a1c88b0642321258bd5462} in fewer than a 7 days:
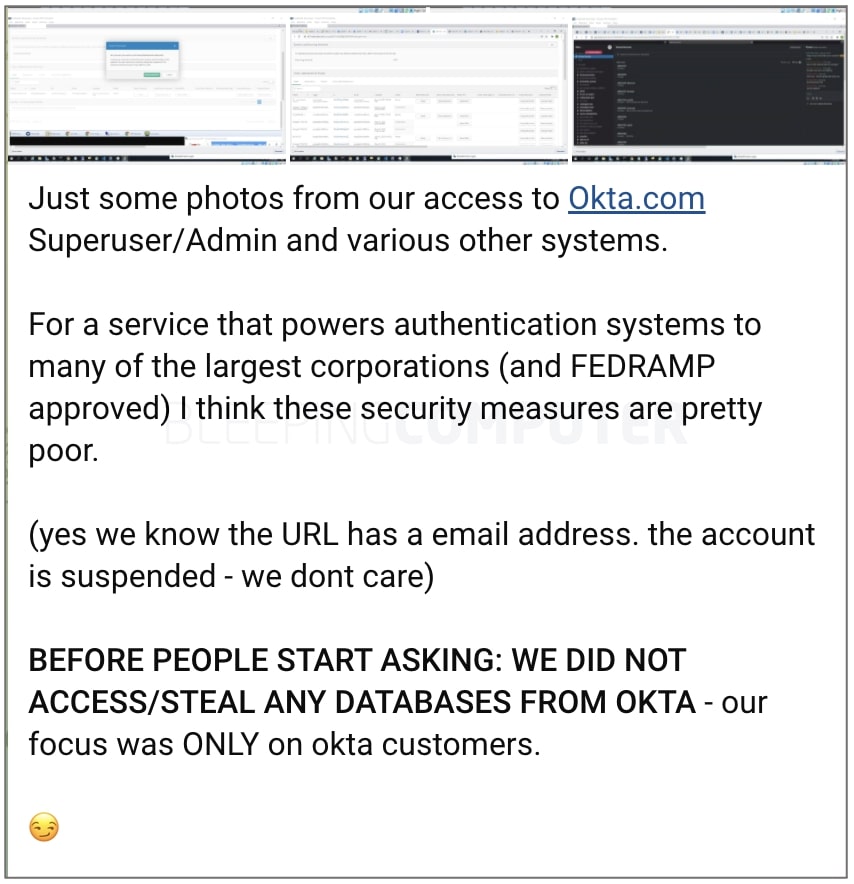
As noted by BleepingComputer this 7 days, Okta had beforehand said it was investigating claims of a hack after Lapsus$ members shared numerous screenshots in a Telegram chat implying they had hacked Okta’s customer networks:
At first, Okta’s CEO Todd McKinnon labeled this incident an “attempt” by risk actors to compromise the account of a assistance engineer. Nevertheless, it later on grew to become clear that 2.5{f5ac61d6de3ce41dbc84aacfdb352f5c66627c6ee4a1c88b0642321258bd5462} of Okta’s customers—366 to be specific, ended up certainly impacted by the incident.
The hack spanned over “a five-day window” between January 16th and 21th, throughout which an attacker attained Distant Desktop (RDP) access to a Sitel guidance engineer’s laptop computer.
The good thing is, Sitel’s assistance engineers, in accordance to Okta, have confined obtain to Jira tickets and support systems but are limited from downloading, creating, or deleting customer records.
“Support engineers are able to facilitate the resetting of passwords and multi-factor authentication components for users, but are not able to decide on people passwords,” clarifies Okta.
In other words and phrases, assist engineers can frequently set off password resets for users but are unable to log in to consumer accounts.
Okta concludes that the screenshots shared by Lapsus$ group were being taken from the Sitel engineer’s compromised account that had limited accessibility.
The enterprise also refuted Lapsus$ group’s declare of obtaining “superuser/admin” obtain, clarifying that the accessibility attained by Lapsus$ remained minimal to an interior Okta assistance software and is not synonymous with “superadmin” accessibility that gives complete obtain to all consumers and method property.
The application employed by Sitel engineers is developed with “least privilege in brain” to make sure that aid engineers have only the specific access they have to have to execute their roles, explains Okta.
No matter, the organization expressed disappointment for the extended time it took for the investigation results to occur out:
“I am tremendously dissatisfied by the lengthy period of time of time that transpired involving our notification to Sitel and the issuance of the full investigation report,” said David Bradbury, Okta’s Main Safety Officer.
“Upon reflection, at the time we received the Sitel summary report we need to have moved more swiftly to realize its implications.”
It’s been a occupied week for Okta’s security teams who expended hrs analyzing more than 125,000 log entries to arrive at an authoritative photo of the cyber incident that occurred two months in the past.
“As with all security incidents, there are numerous alternatives for us to improve our processes and our communications. I am confident that we are going in the ideal path and this incident will only provide to reinforce our dedication to safety,” concludes Bradbury.
