About the Writer
Jeremy Van der Haegen is a Belgian freelance journalist who covers small business and politics of the Asia-Pacific, cryptocurrencies, and blockchain engineering.
A person of the most disregarded problems of blockchain techniques is their ability to resist the rapidly-evolving machines recognised as quantum computers.
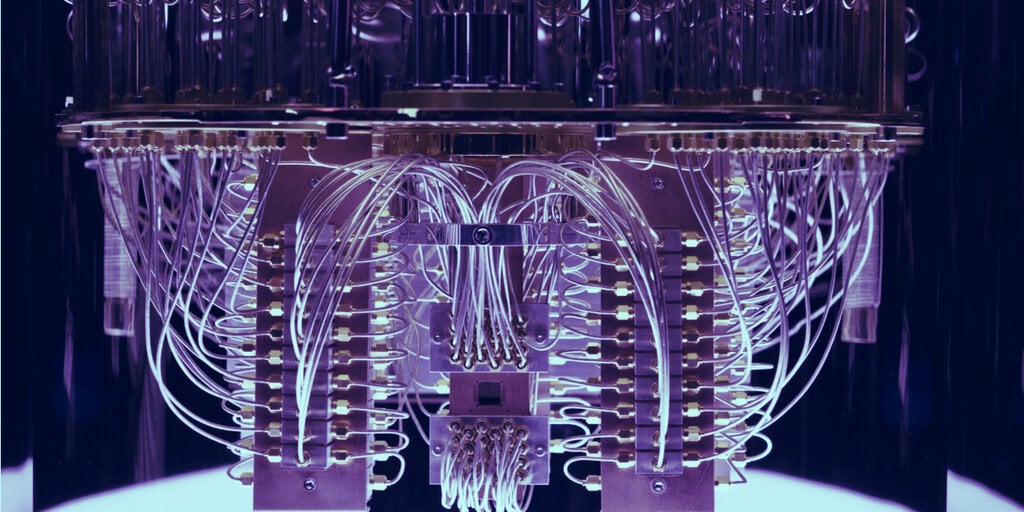
These powerful desktops use quantum physics to resolve complex troubles that are outside of the attain of common units by employing qubits—an evolution of the basic binary little bit. Qubits are in a position to stand for the price 1 or at the same time, which promises to deliver an exponential raise of computing ability.
The world’s major superpowers are pouring billions of pounds into the enhancement of this technology—and for fantastic cause. The initially country or company to harness quantum computing will be poised to crack the encryption defending rivals’ delicate files.
In the case of blockchain devices, the cryptography protecting their tamper-evidence ledgers may perhaps be at chance. Scientists at the College of Sussex approximated in February that a quantum computer system with 1.9 billion qubits could essentially crack the encryption safeguarding Bitcoin in a mere 10 minutes. Just 13 million qubits could do the work in about a working day.
Fortuitously, the capacity to deploy quantum pcs with so a lot of qubits continue to appears numerous a long time away. IBM unveiled its 127-qubit processor just past calendar year, even though a unit sporting 1,000 qubits is set to be concluded by the close of 2023.
“We’re not there nevertheless,” claimed Jens Groth, a Danish professor in cryptology and encryption researcher at Dfinity. “Nobody is aware of what the correct time body seems like, but blockchain may well only be at risk in just 10 to 20 yrs.”
Groth underlines that there is an important difference between two styles of qubits—physical and reasonable ones. The latter describes a qubit that achieves a superposition among 1 and via a quantum gate. A rational qubit consists of 9 actual physical qubits. “Company announcements about a novel qubit milestone typically issue bodily qubits, not logical ones,” he describes.
Defenders have the upper hand
Whilst scientists like Groth really do not classify quantum desktops as an rapid danger to blockchain technological innovation, experimentation with solutions is yet ongoing. “Cryptographers do mirror on what a suited countermeasure would glimpse like,” Groth states.
Blockchain builders have a obvious advantage in the race to protect in opposition to mounting computing electrical power. Especially, they can boost the range of digits in the cryptographic keys that guard the chain—a procedure that’s quicker to scale than it is for the attackers to catch up. “The defenders are winning this battle in the extensive operate,” Groth statements.
This is apparent in the area of symmetric critical encryption when analyzing the preferred Highly developed Encryption Common (AES). The most common variation of 128 keys could be cracked by quantum computers and even traditional attackers. Nevertheless the AES 256 variation, showcasing 2 times the amount of keys, seems potent plenty of to fend off brute drive assaults by quantum machines for the foreseeable potential.
Some cryptographers, however, are careful about deeming encryption the automated winner in a post-quantum globe. “It’s very difficult to predict irrespective of whether we will deal with to continuously scale up vital dimensions in opposition to effective quantum pcs,” claims Angshuman Karmakar, a investigate affiliate at the Computer system Protection and Industrial Cryptography group (COSIC) of the KU Leuven.
“You normally have to take a pessimistic solution when you are on the defending aspect. A new brilliant algorithm could pop up and all of a sudden put attackers at an edge. The likelihood of this occurring is extremely small, but can never ever be ruled out,” Karmakar claims.
Meanwhile, lattice-centered cryptography delivers a different potential solution to quantum attacks. This variety of encryption adds mathematical sounds that could even confuse a futuristic supercomputer. “Quantum personal computers could come across a needle in a haystack by frequently doubling the chance of locating it. You need to design constructions that these computers cannot acquire benefit of,” Groth says.
According to Karmakar, lattice-primarily based answers are currently in the approach of standardizing and must be prepared for general public use quickly. “A lot will rely on how rapidly the field can apply new encryption. On the other hand, there is a good deal of time remaining prior to quantum computers access a level exactly where they could crack a blockchain,” he says.
Switching to a new personal critical
Implementing an encryption up grade for a blockchain program would seem to be the greatest headache for cryptographers. In a usual blockchain like Bitcoin, each and every node will have to be certain to swap to a new encryption system. Governance protocols like the Net Personal computer could routinely update their technique as a result of user voting. Collective determination will be crucial in all conditions.
The method of upgrading present private keys, nevertheless, could generate new vulnerabilities. That is simply because, in accordance to Groth, new keys will be generated by the program after effectively utilizing submit-quantum encryption. To activate a swap to the new important, buyers will have to signal for acceptance with their old just one.
Even so, inactive people could by no means improve their non-public crucial, which could induce major troubles. Sizable dormant wallets, like the types that contains all around 1 million Bitcoins that supposedly belong to Satoshi Nakamoto, possible will in no way see an encryption improvement. This could leave sure legacy portions of the crypto ecosystem open to quantum-based mostly attacks even if the blockchain they depend on has been safely and securely upgraded.
The bottom line is, though blockchains appear secure for now from quantum computing, builders will have to have to remain vigilant and be prepared to acquire new measures to be certain this stays genuine.
Want to be a crypto expert? Get the best of Decrypt straight to your inbox.
Get the most significant crypto information stories + weekly roundups and more!
