
BlackCat (ALPHV) claims Swissport ransomware attack, leaks data

The BlackCat ransomware group, aka ALPHV, has claimed obligation for the current cyber attack on Swissport that induced flight delays and assistance disruptions.
The €3 billion revenue organization, Swissport, has a existence across 310 airports in 50 nations around the world and provides cargo dealing with, servicing, cleaning, and lounge hospitality solutions.
BlackCat has now been viewed by BleepingComputer to leak a minuscule set of terabytes of data supposedly obtained from the modern ransomware attack.
BlackCat starts leaking data
As documented by BleepingComputer, the cargo and hospitality solutions giant had previously disclosed a ransomware attack on its units.
Currently, BlackCat (ALPHV) ransomware group has posted a little established of sample documents that the team promises to have obtained from Swissport.
The risk actor has announced they are inclined to sell the entire 1.6 TB “facts dump” to a possible consumer:
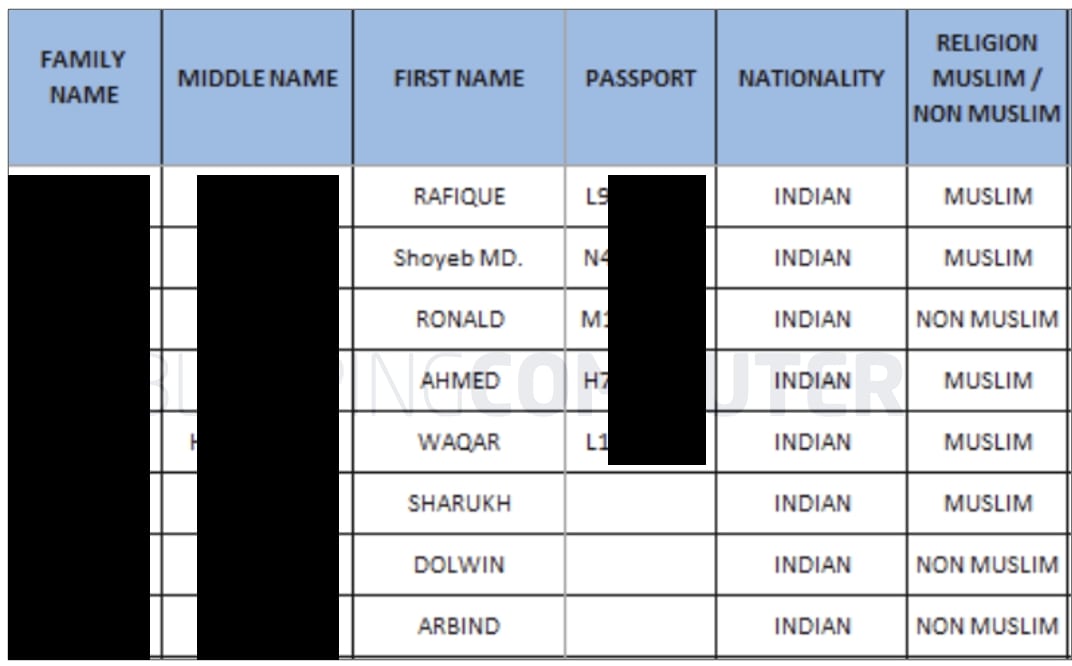
The knowledge leak web site viewed by BleepingComputer now incorporates visuals of passports, inside enterprise memos, and what look to be aspects of job candidates, this sort of as their:
- Comprehensive identify
- Passport Number
- Nationality
- Religion (Muslim or Non-Muslim indicator)
- E mail
- Cellular phone range
- Task job, interview scores, and other recruitment information
BleepingComputer has reached out to Swissport to better have an understanding of what this info signifies, notably the flag indicator recording the religion of work candidates:
With its 66,000 employees throughout the world, Swissport handles 282 million passengers and 4.8 million tons of cargo every single yr, generating it a vital connection in the international aviation vacation market chain.
As these types of, even though the cyberattack on Swissport was “largely contained” with systems fully cleaned and restored, inquiries continue being as to what takes place to delicate information that threat actors may perhaps have gotten their hands on.
BlackCat emerged after BlackMatter’s shut down
Dubbed the “most advanced” ransomware group of 2021, BlackCat ransomware team emerged after BlackMatter’s shut down by legislation enforcement.
This month, BlackCat members confirmed they are indeed linked to the BlackMatter/DarkSide operation.
Even though the ransomware gang phone calls on their own ALPHV, stability researcher MalwareHunterTeam previously named the ransomware BlackCat after the team used the image of a black cat on each individual victim’s Tor payment webpage. Since then, the ransomware procedure has been recognized as BlackCat when talked over in the media or by protection researchers.
BleepingComputer is knowledgeable of multiple victims qualified by this ransomware gang considering the fact that November 2021 from a lot of international locations, together with the United states, Australia, and India.
Ransom calls for commonly vary among $400,000 to $3 million payable in Bitcoin or Monero. Victims paying out in bitcoin incur an supplemental 15{f5ac61d6de3ce41dbc84aacfdb352f5c66627c6ee4a1c88b0642321258bd5462} fee on major of the demanded ransom.
As an more extortion technique, the BlackCat threat actors threaten to DDoS victims until eventually they pay out a ransom.
Total, this is a remarkably subtle ransomware procedure with the danger actors plainly looking at all areas of attacks.
