Are quantum computers about to break online privacy?

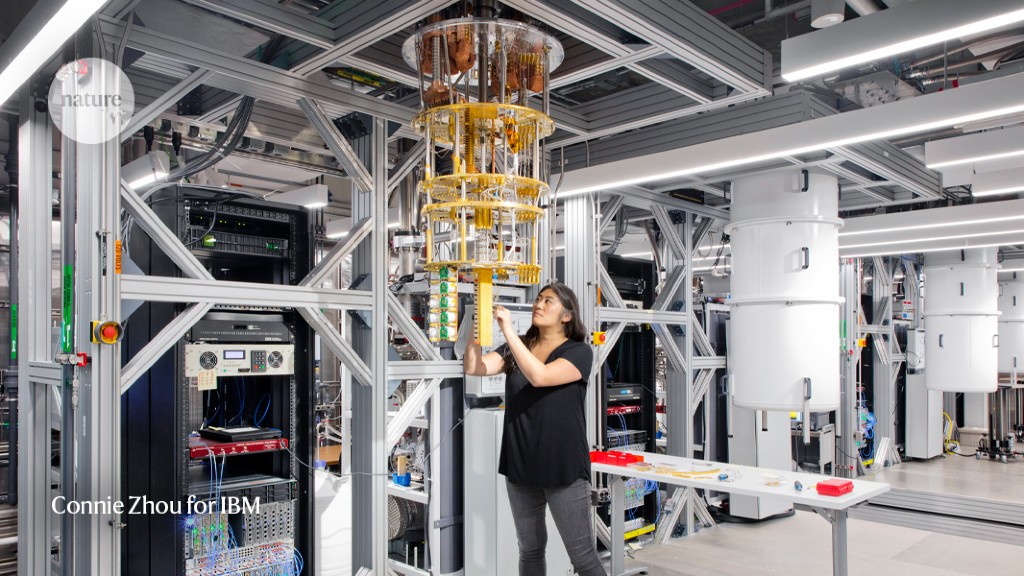
A quantum personal computer at IBM’s Thomas J. Watson Exploration Center.Credit score: Connie Zhou for IBM
A workforce of scientists in China has unveiled a strategy that — theoretically — could crack the most commonly employed forms of electronic privateness working with a rudimentary quantum computer system.
The system worked in a modest-scale demonstration, the researchers report, but other experts are sceptical that the technique could scale up to conquer everyday computers at the task. Nevertheless, they warn that the paper, posted late very last thirty day period on the arXiv repository1, is a reminder of the vulnerability of on the internet privacy.
Quantum computers are known to be a potential danger to recent encryption programs, but the technologies is still in its infancy and scientists typically estimate that it will be several many years right until they can be faster than standard personal computers at cracking cryptographic keys.
Scientists recognized in the 1990s that quantum computers could exploit peculiarities of physics to execute jobs that appear to be to be past the achieve of ‘classical’ computers. Peter Shor, a mathematician now at the Massachusetts Institute of Technologies in Cambridge, confirmed in 19942 how to apply the phenomena of quantum superposition and interference to factoring integer numbers into primes — the integers that simply cannot be further more divided devoid of a remainder.
Shor’s algorithm would make a quantum computer exponentially faster than a classical a single at cracking an encryption program based mostly on significant primary quantities — identified as RSA just after the initials of its inventors — as nicely as some other well-known cryptography methods, which now secure online privateness and security. But applying Shor’s method would need a much greater quantum pc than the prototypes accessible. The measurement of a quantum laptop or computer is measured in quantum bits, or qubits scientists say it might consider a million or a lot more qubits to crack RSA. The major quantum equipment readily available currently — the Osprey chip introduced in November by IBM — has 433 qubits.
Shijie Wei at the Beijing Academy of Quantum Data Sciences and collaborators took a distinct route to defeat RSA, centered not on Shor’s but on Schnorr’s algorithm — a procedure for factoring integer figures devised by mathematician Claus Schnorr at Goethe College at Frankfurt, Germany, also in the 1990s. Schnorr’s algorithm was made to operate on a classical laptop, but Wei’s crew executed part of the course of action on a quantum personal computer, applying a process termed quantum approximate optimization algorithm, or QAOA.
In the paper, which has not nonetheless been peer-reviewed, they claim that it could crack powerful RSA keys — numbers with much more than 600 decimal digits — working with just 372 qubits. In an e-mail to Character on behalf of all the authors, Guilu Lengthy, a physicist at Tsinghua College in China, cautioned that getting several qubits is not enough, and that recent quantum machines are continue to also-mistake susceptible to do these kinds of a significant computation correctly. “Simply rising the qubit variety without having decreasing the mistake charge does not help.”
The workforce shown the technique on a 10-qubit quantum laptop to component the additional-manageable, 15-digit amount 261,980,999,226,229. (It splits into two primes, as 15,538,213 x 16,860,433.) The scientists say this is the major selection yet to have been factored with the support of a quantum computer — although it is much smaller sized than the encryption keys utilised by modern-day world-wide-web browsers.
The hassle is, no one appreciates if the QAOA will make factoring substantial numbers more rapidly than just running Schnorr’s classical algorithm on a notebook. “It must be pointed out that the quantum speedup of the algorithm is unclear,” publish the authors. In other phrases, when Shor’s algorithm is confirmed to break encryption successfully when (and if) a massive-ample quantum computer system results in being obtainable, the optimization-primarily based approach could operate on a considerably more compact machine, but it might hardly ever complete the endeavor.
Michele Mosca, a mathematician at the College of Waterloo in Canada, also points out that the QAOA route is not the to start with quantum algorithm known to be able to element full figures working with a small variety of qubits. He and his collaborators explained3 one in 2017. So, researchers presently understood that there is absolutely nothing essential that necessitates quantum personal computers to be quite massive to component numbers.
Other scientists have complained that even though the newest paper could be proper, the caveat concerning speed will come only at the pretty conclusion of it. “All told, this is 1 of the most deceptive quantum computing papers I’ve viewed in 25 years,” blogged quantum computing theorist Scott Aaronson at the University of Texas at Austin.
In the e-mail, Very long says that he and his collaborators strategy to change the paper and to go the caveat increased up. “We welcome the peer critique and the interaction with researchers all over the globe,” the assertion included.
Even if the Schnorr-centered technique will not split the World wide web, quantum computers could finally do so by jogging Shor’s algorithm. Safety scientists have been active developing a variety of alternate cryptographic devices that are viewed as much less probably to succumb to a quantum attack, termed post-quantum or quantum-safe. But scientists may also find out much better quantum algorithms in the long term that beat these programs, with calamitous repercussions.
“Confidence in electronic infrastructures would collapse,” says Mosca. “We’d all of a sudden switch from handling the quantum-risk-free migration by way of engineering lifecycle management to crisis administration,” he adds. “It will not be really any way you slice it.”
